BrowserDefend Research: Advancing Phishing Detection with Next-Generation Fingerprinting (v2.0)
At BrowserDefend, we’re continuously evolving our methods to stay ahead of emerging threats. Our latest research project is focused on enhancing the detection capabilities of phishing landing pages—a critical step toward our upcoming v2.0 system.
The Evolution of Phishing Fingerprinting
Our current implementation leverages fingerprinting techniques to identify phishing pages by analyzing key elements of a page’s structure and scripts. While this method has served us well, the ever-changing tactics of cybercriminals demand continuous innovation.
Introducing v2.0: A New Approach to Grouping Phishing Pages
Our next-generation solution goes beyond simple fingerprinting. Key improvements include:
- Enhanced Structural Analysis: We analyze underlying HTML, JavaScript, and asset structures to capture the true “signature” of a phishing kit—even when superficial details differ.
- Fuzzy Hashing Techniques: By employing fuzzy hashing methods that generate resilient content fingerprints, we can group pages that are near-duplicates despite minor modifications.
- Optimized Clustering for Scale: Our incremental clustering techniques reduce computational overhead, ensuring rapid detection even as our dataset grows.
Research in Practice: What We’re Testing
Without revealing every technical detail, here’s a glimpse into our process:
- HTML Structure Fingerprinting: Extracting structural elements—such as form layouts and tag hierarchies—to create a unique blueprint of each page.
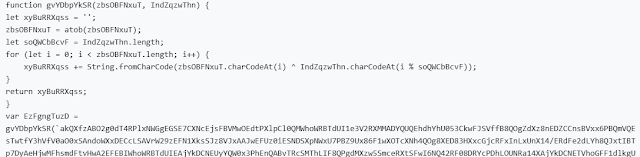
- Analyzing JavaScript and Obfuscation: Identifying common obfuscation techniques and reused scripts that link pages together.
- Fuzzy Hashing for “Near-Duplicate” Detection: Implementing lightweight, fuzzy hashing (inspired by SimHash) to tolerate minor changes while retaining similarity signals.
What This Means for Our Clients
With our advanced detection engine, BrowserDefend will be able to:
- Detect Threat Actor Campaigns Faster: Rapidly identify clusters of phishing pages to block entire campaigns in real time even when heavily obfuscated.
- Improve Threat Attribution: Map related pages to known threat actors, enhancing targeted countermeasures, and providing insights to security researchers.
- Adapt to Evolving Tactics: Stay one step ahead as cybercriminals refine their methods.
Looking Forward
This research project represents a major step forward in our mission to secure the web. While our current fingerprinting methods have provided a strong foundation, the enhancements introduced in v2.0 will enable a more nuanced, efficient, and scalable approach to phishing detection.
At BrowserDefend, we’re dedicated to continuous innovation. Stay tuned for further updates on our cutting-edge techniques and how they will help safeguard your digital environment.
Conclusion
By leveraging advanced structural analysis, fuzzy hashing, and optimized clustering, our upcoming v2.0 system will more effectively identify and group phishing landing pages by threat actor. This breakthrough will enable faster detection, improved threat attribution, and a proactive defense against emerging phishing threat actors.
For more details on our research and how BrowserDefend can help protect you, visit BrowserDefend.com.



Comments
Post a Comment